Recent NCUA examination feedback points to a practical supervisory theme: GLBA-driven Information Security Risk Assessments should continue to evolve with the threat environment. A stronger ISRA should not stop at traditional perimeter, access, vendor, and disaster recovery topics. Credit unions should be ready to document how artificial intelligence, ransomware, insider threats, social media usage, and cloud storage services affect member information, controls, testing, and residual risk.
This is not about rebuilding the ISRA from scratch. It is about reviewing current documentation, identifying missing threat areas, and adding discussion items, recommendations, or enhancements where the risk assessment no longer reflects current exposure.
If you have questions about updating your ISRA for current NCUA examination focus areas, please reach out to the NETBankAudit team.
Why GLBA ISRA Documentation Matters for NCUA Examination Readiness
The issue is not a new framework. It is whether current threats are clearly documented.
The baseline starts with GLBA Section 501(b), which requires standards for safeguards that protect customer information. In the credit union context, that means protecting member information from anticipated threats and unauthorized access.
12 CFR Part 748, Appendix A carries those safeguarding expectations into the credit union environment through requirements for an information security program, periodic risk assessments, controls, testing, and board reporting. For compliance teams, the ISRA should do more than repeat prior-year language.
NCUA’s Information Security Examination and Cybersecurity Assessment Program focuses examiner review on information security programs, risk management, and controls. That focus supports a direct connection between risk assessment results, control design, testing, and reporting.
The five areas below do not create a separate ISRA process. They should be incorporated into the existing GLBA risk assessment based on actual usage, exposure, controls, and residual risk. If an area is missing, management should consider whether it belongs in the ISRA as a risk entry, discussion item, recommendation, or planned enhancement.
Five Emerging Threat Areas Credit Unions Should Review in the ISRA
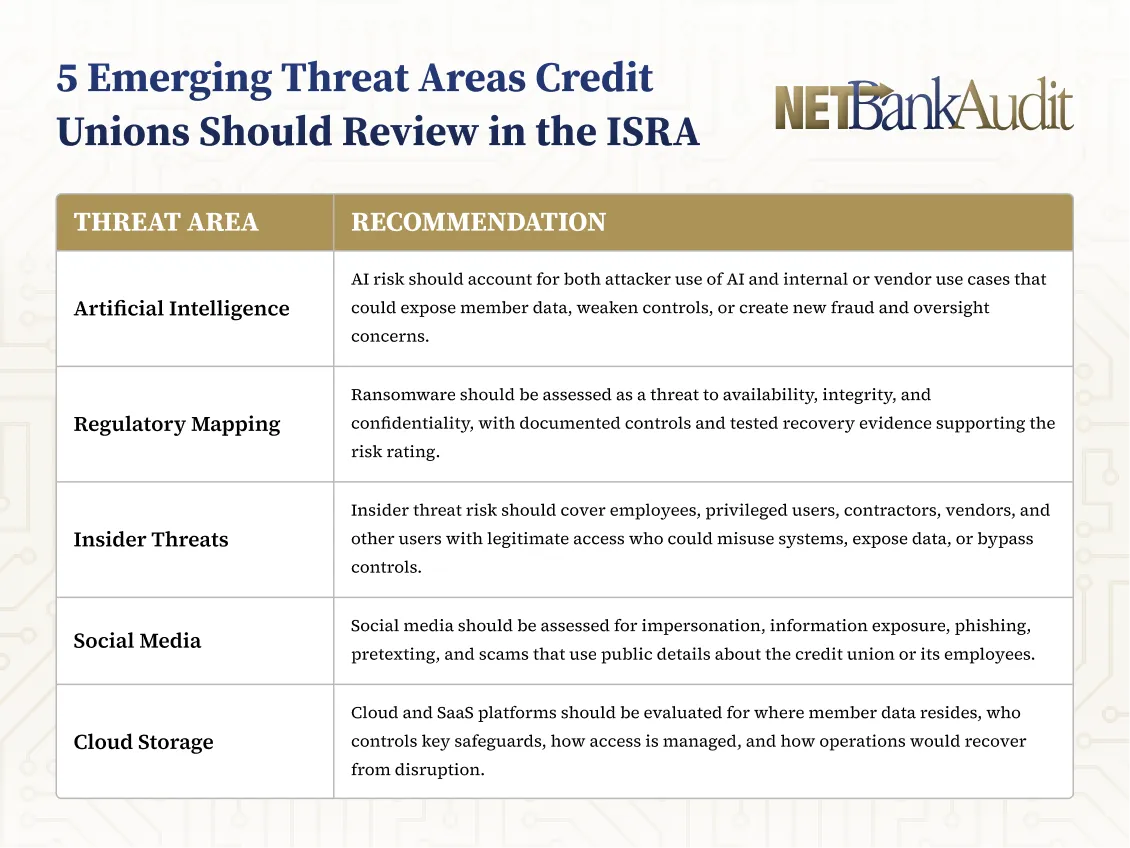
1. Artificial intelligence risk should address data leakage, fraud, and unvetted tools
AI should be evaluated from two directions. Attackers can use it to support phishing, spoofing, credential harvesting, social engineering, malware development, and deepfake-enabled fraud. At the same time, credit unions or vendors may use AI for member service, fraud detection, underwriting, operations, monitoring, reporting, or staff productivity.
NCUA artificial intelligence resources address AI implementation, risk management, data security, use cases, and cybersecurity risks. That distinction matters because AI is not only an innovation topic. It can affect member information, fraud controls, vendor oversight, access monitoring, and incident response.
ISRA documentation should identify actual AI use cases, vendor-provided tools, experimental uses, and prohibited uses. Public or unvetted AI tools deserve specific attention if employees could enter member information, internal procedures, confidential operational details, or source material into prompts.
The assessment should also consider AI-enabled phishing, deepfake wire fraud attempts, prompt injection, model or data manipulation, and unauthorized access to AI-related datasets. The strongest entries connect each scenario to affected systems, data types, business processes, control owners, training, monitoring, and vendor oversight.
2. Ransomware risk should link encryption threats to recovery evidence
Ransomware remains a high-impact threat because it can affect availability, integrity, and confidentiality at the same time. A ransomware event may disrupt core processing, online banking, payments, call center operations, ATM services, or shared vendor platforms. It may also involve data theft, not just system encryption.
The ISRA should identify ransomware as a specific external threat vector. Common delivery paths include phishing, remote access compromise, exploitation of vulnerabilities, and vendor compromise. The documentation should also describe how ransomware could affect critical systems that support member data and financial operations.
Control documentation should move beyond general statements such as “anti-malware is in place.” Stronger entries identify layered controls, including patch management, endpoint detection and response, multi-factor authentication, least privilege, privileged access monitoring, network segmentation, secure configurations, backup protection, and tested restoration procedures.
Recovery capability should be supported by evidence. A credit union may have backups, but the ISRA should consider whether restoration has been tested, whether backup repositories are protected, and whether ransomware playbooks have been exercised. Tabletop exercises, technology recovery tests, vulnerability assessments, and penetration test results can support the control effectiveness rating.
3. Insider threats should include malicious, negligent, and third-party users
Insider threat risk fits naturally within GLBA because insiders may already have legitimate access to systems that store, process, transmit, or display member information. The risk includes malicious activity, but it also includes errors, policy violations, weak security habits, and compromised credentials.
An ISRA aligned with examiner expectations should analyze privileged users, general staff, contractors, vendor administrators, managed service providers, and other third-party users with access to credit union systems. Privileged users present higher risk because they may be able to extract data, change configurations, disable controls, or alter logs.
Control expectations include access governance, least privilege, timely provisioning and de-provisioning, periodic access reviews, segregation of duties, change management, logging, SIEM monitoring, user behavior alerting, and acceptable use policies. Training should also address social engineering, phishing, remote work, data handling, and restrictions on AI or cloud tools.
The most useful insider threat entries are scenario-based. Examples include unusual data downloads, after-hours access, improper use of file sharing tools, or a vendor administrator retaining access after a contract change. Each scenario should lead to a risk rating, control assessment, and remediation decision where needed.
4. Social media usage should be evaluated as a social engineering entry point
Social media risk is often underestimated because it may not appear as a separate line item in older ISRA templates. Even so, it fits within social engineering, information exposure, impersonation, and member scam risk. Attackers can use public information to make phishing, pretexting, and spoofing attempts more convincing.
Credit unions should consider both official accounts and employee activity. Official credit union accounts can be impersonated or abused to mislead members. Employee profiles and posts may expose job titles, email formats, reporting relationships, vendor relationships, branch details, travel patterns, or operational clues.
The risk assessment should also consider AI-enabled data mining. Publicly available information can be collected and analyzed at scale to identify employees, relationships, assets, and likely targets. That information can support social engineering attempts against staff or scams directed at members.
ISRA documentation should describe policies for official accounts, employee acceptable use guidance, posting approval practices, monitoring for fake accounts, escalation procedures, member reporting channels, and training. Security awareness activities should include social media-based phishing, pretexting, impersonation, and deepfake scenarios where appropriate.
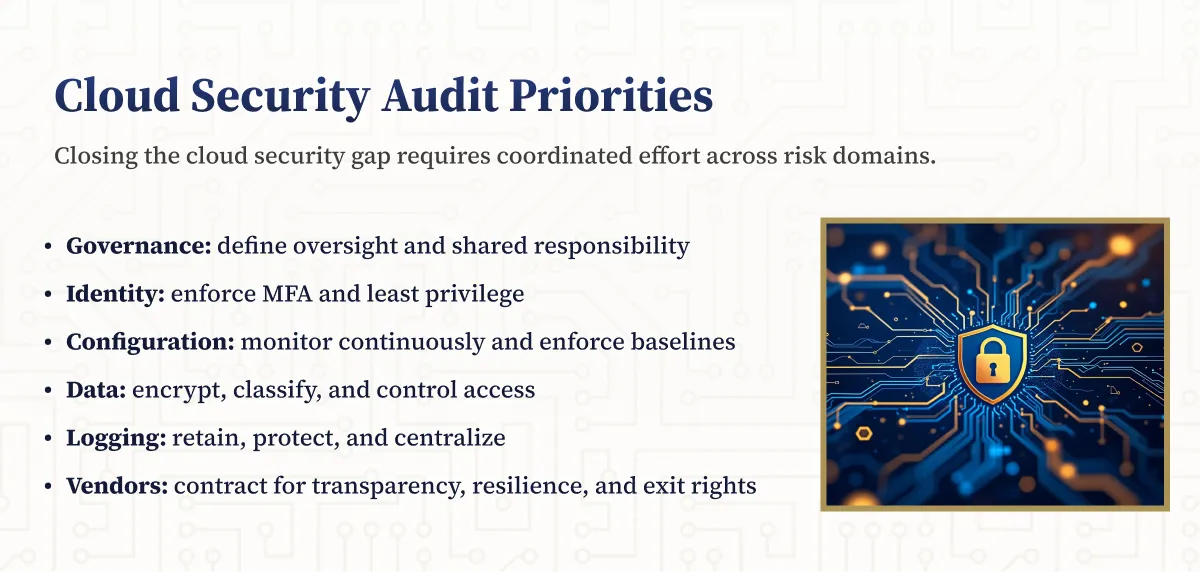
5. Cloud storage risk should focus on data mapping, shared responsibility, and resiliency
Cloud storage, SaaS platforms, collaboration tools, document repositories, backup providers, and file sharing services should be treated as part of the information system inventory. A credit union should know what member information resides in each platform, who can access it, how it is protected, and how service disruption would affect operations.
The FFIEC cloud computing statement highlights risk management practices for safe and sound cloud use, including safeguards to protect sensitive information from consumer harm. This is useful context for ISRA documentation because cloud risk often crosses vendor management, access control, data protection, and business continuity.
Cloud ISRA entries should include data classification and mapping, shared responsibility analysis, vendor due diligence, contractual protections, security controls, resiliency expectations, and exit planning. Shared responsibility should be specific. The assessment should distinguish whether the credit union or provider handles access control, encryption, patching, logging, backup, and recovery.
Resiliency is especially important because third-party outages and ransomware events can affect member service. The ISRA should evaluate business continuity and disaster recovery capabilities, geographic redundancy, recovery objectives, testing frequency, incident notification, SOC reports, data portability, alternate providers, and the ability to restore from independent backups.
What Credit Unions Should Do Before the Next NCUA Examination
A focused ISRA refresh can close common documentation gaps
Credit unions do not need to turn a targeted exam insight into an oversized rewrite. In many cases, the better approach is to update existing risk records, add missing scenarios, and improve the evidence trail. The review should focus on whether the ISRA clearly shows risk identification, control evaluation, testing, residual risk, and governance.
If a topic is missing entirely, management should treat that omission as an enhancement opportunity. If a topic is mentioned only generally, management should determine whether the documentation is specific enough for examiner review. This is especially important when a threat affects member information, third-party providers, privileged access, or service availability.
Before finalizing the ISRA, confirm that each material threat can be traced to affected systems, member information, vendors, controls, testing, and management action. The goal is not length. The goal is clear documentation that shows management considered current threats and made risk-based decisions.
- Confirm whether the ISRA explicitly addresses AI, ransomware, insider threats, social media usage, and cloud storage services where those topics are applicable to the institution.
- Add missing topics as risk entries, discussion items, recommendations, or planned enhancements. Include realistic scenarios such as AI-enabled phishing, deepfakes, ransomware data theft, privileged user misuse, social media impersonation, and cloud resiliency concerns.
- Tie each topic to affected systems, member information, vendors, business processes, control owners, and relevant controls, including access control, monitoring, backup restoration, incident response, training, and vendor oversight.
- Document residual risk, remediation owners, target dates, and formal risk acceptance where needed, using factors such as member harm, operational disruption, fraud exposure, compliance impact, financial loss, and service availability.
- Summarize material changes, testing results, residual risks, vendor dependencies, and management actions for board or committee reporting. Board or committee records should show awareness of significant risk decisions.
How NETBankAudit Can Help Strengthen GLBA ISRA Documentation
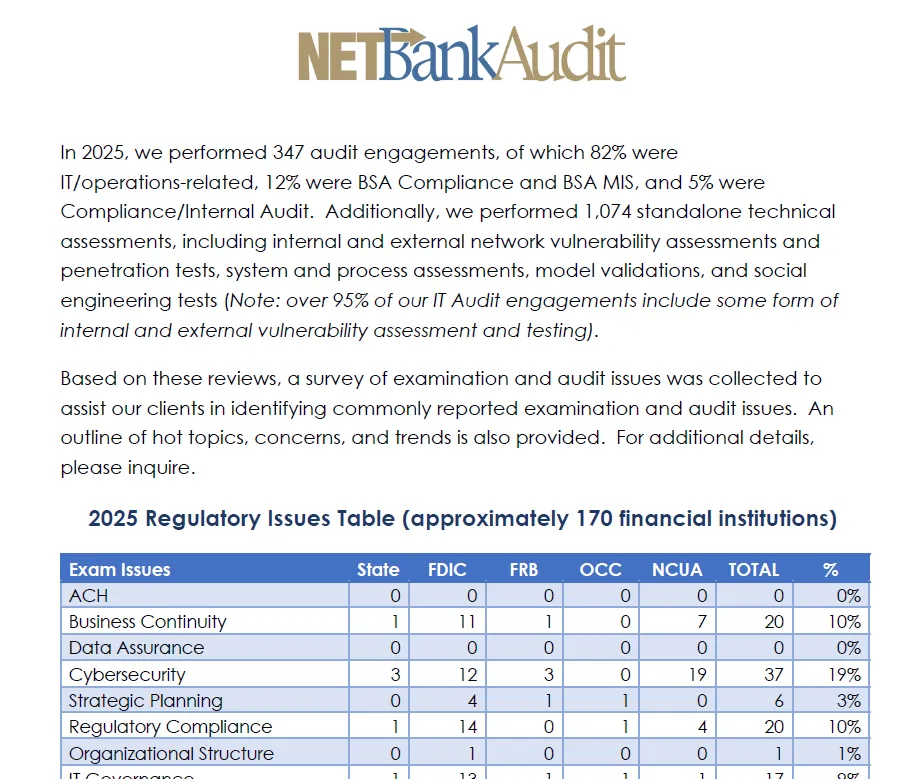
NETBankAudit reviews cybersecurity and information security risk assessments and programs against FFIEC guidelines, industry standards, GLBA 501(b), and other regulatory expectations. Its review approach considers information security governance, cybersecurity controls, external dependency management, incident response, resilience, testing, and management oversight.
NETBankAudit also offers GLBA 501(b) Information Security Risk Assessments, Cybersecurity Controls Evaluations, ransomware assessments, vendor management risk assessments, social media risk assessments, cloud security control reviews, penetration testing, and social engineering testing. These services help financial institutions identify gaps, validate controls, and strengthen documentation before examination activity.
If your credit union needs help updating its GLBA/ISRA for AI, ransomware, insider threats, social media, cloud storage, or broader NCUA examination readiness, contact NETBankAudit.
%201%20(1).svg)
%201.svg)
.avif)

.svg)
%201.webp)



.webp)
%20(1).webp)

.webp)

.webp)
.webp)
.png)

.webp)

.webp)











.webp)



.webp)

%201.webp)
.webp)
%20(3).webp)


.webp)


%20Works.webp)

.webp)




.webp)
%20(1).webp)

.webp)










.webp)
.webp)

.webp)
.webp)
.webp)
.webp)
.webp)
.webp)
%201.svg)