Ransomware attacks on financial institutions have evolved into highly sophisticated, multi-stage operations. This article deep-dives into the most active ransomware gangs: LockBit, Scattered Spider, RansomHub, Akira, Play, BianLian, and Royal/BlackSuit. Each section details the group’s tactics, infection chains, and specific risks to the financial sector, followed by actionable audit and risk management recommendations.
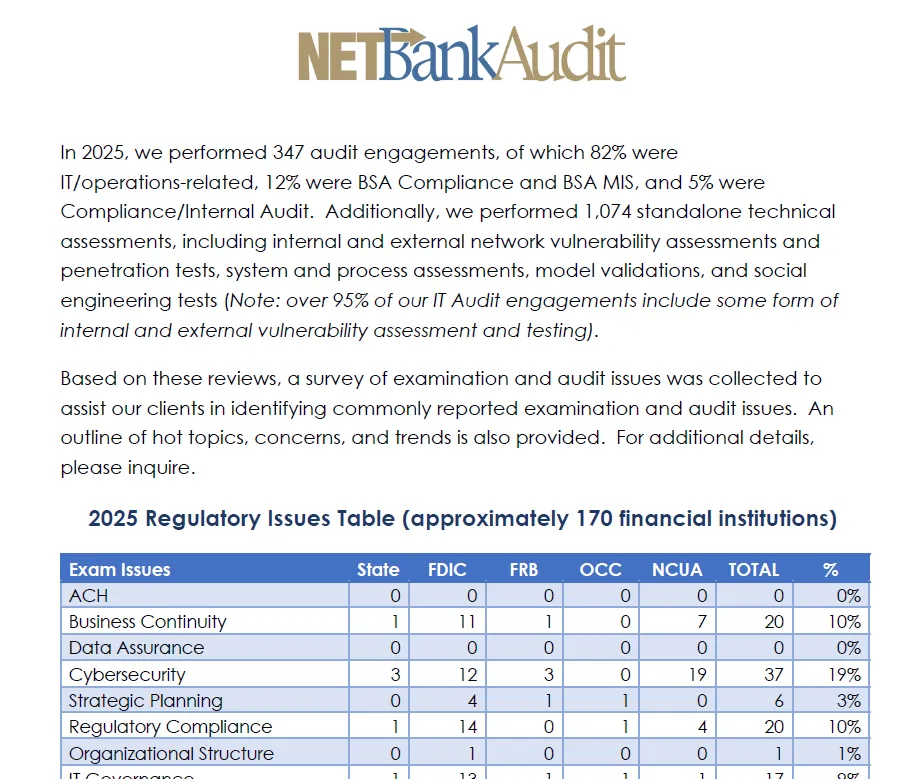
NETBankAudit’s senior auditors and engineers have decades of experience in advanced penetration testing, social engineering, and ransomware risk assessments for financial institutions. If you need a comprehensive cybersecurity audit or a crypto-asset safeguarding risk assessment, contact our team for expert guidance.

Major Ransomware Gangs Targeting Financial Institutions
LockBit: Modular RaaS, Fast Encryption, and Persistent Threat
Infection Chain and Initial Access
LockBit affiliates typically exploit exposed RDP or VPN endpoints, or use phishing campaigns to gain initial access. Once inside, they deploy a password-protected downloader to evade signature-based detection, then execute the LockBit payload. The malware checks system language to avoid running in certain regions (e.g., Russian, Arabic), and uses rapid, multi-threaded encryption to minimize detection windows1,2,3,5.
Double Extortion and Data Exfiltration
LockBit’s double-extortion model involves exfiltrating sensitive data (using tools like StealBit or cloud storage) before encrypting files. The group’s ransom notes direct victims to a Tor portal for negotiation, with demands often in the millions and payable in cryptocurrency. The encrypted files carry a .lockbit (or similar) extension.
LockBit’s Impact on Financial Institutions
LockBit’s infrastructure was disrupted in 2024 by Operation Cronos, but the group quickly rebranded and resumed operations. Affiliates continue to target financial institutions, leveraging the sector’s low tolerance for downtime and data leaks. The FBI estimates over 1,000 U.S. victims in 2024 alone, with LockBit’s rapid encryption and affiliate model making it a persistent threat even after law enforcement actions.
Scattered Spider: Social Engineering and Credential Abuse
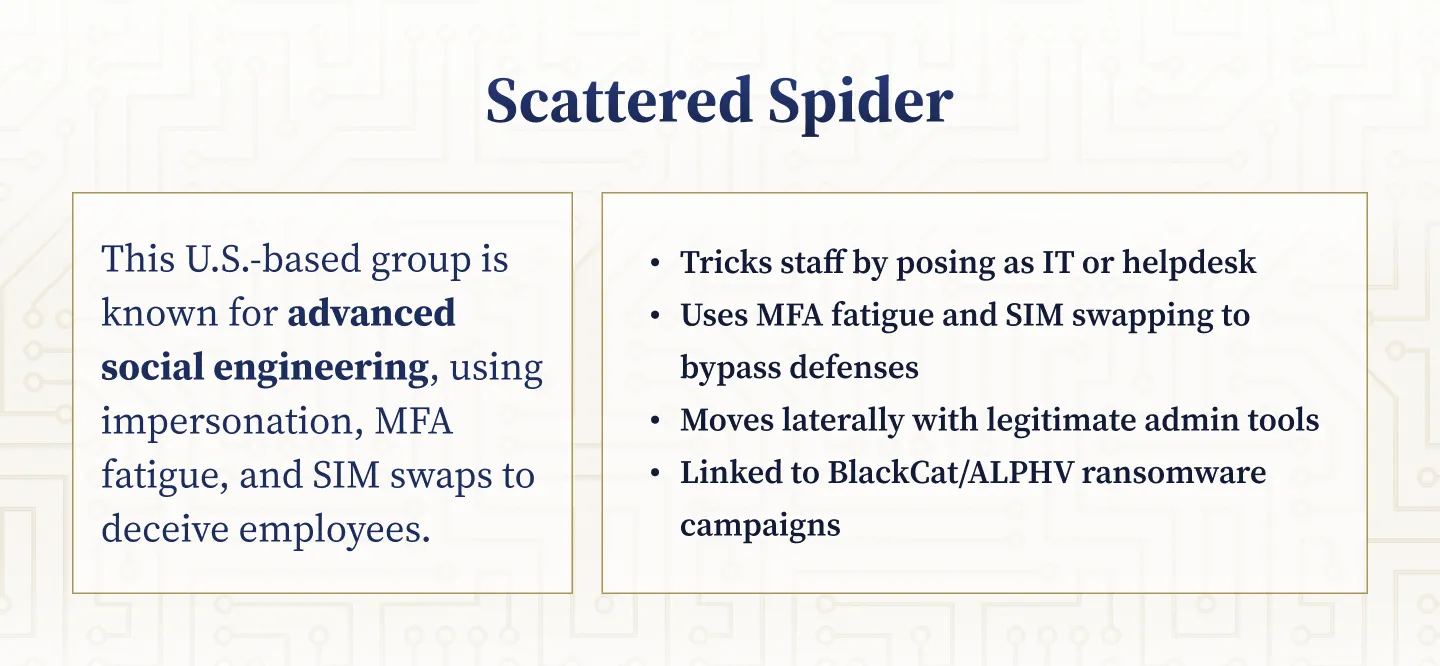
Social Engineering Tactics
Scattered Spider (Starfraud, UNC3944, Muddled Libra) is a U.S.-origin group specializing in social engineering and credential-based attacks. Operators impersonate IT or helpdesk staff via phone, SMS, or email, tricking employees into running remote-access tools or divulging credentials. They are adept at “MFA fatigue” (repeatedly sending MFA prompts) and SIM-swapping to bypass two-factor authentication2,4,5.
Post-Exploitation and Lateral Movement
Once inside, they use legitimate admin tools (Fleetdeck, Pulseway, Splashtop) for lateral movement and data exfiltration. Scattered Spider has been linked to high-profile breaches in retail, entertainment, and business services, and has deployed BlackCat/ALPHV ransomware in some cases.
Scattered Spider’s Financial Sector Impact
The group’s focus on human factors makes them especially dangerous for financial institutions with large support teams or remote workforces. In 2024, U.S. authorities charged several members, but the group’s tactics remain a top concern for banks and credit unions.
RansomHub: Rapidly Evolving Double-Extortion
Infection Chain and Initial Access
RansomHub, first observed in early 2024, is a RaaS variant that quickly attracted affiliates from LockBit and ALPHV. Its infection chain often starts with phishing, public-facing server exploits, or password spraying. Affiliates exfiltrate sensitive data, encrypt network systems, and threaten to publish stolen information if ransoms are not paid6.
Negotiation and Payment
RansomHub’s ransom notes provide a client ID and Tor site for negotiation, with demands ranging from small sums to multimillion-dollar payments in cryptocurrency. The group is known for leveraging zero-day exploits (e.g., Fortinet VPN bugs) and stolen credentials, and for using “StealBit”-style exfiltration.
RansomHub’s Financial Sector Targeting
RansomHub has already targeted over 210 victims, including U.S. financial firms and brokerage houses. The FBI and MS-ISAC have issued advisories urging financial institutions to patch internet-facing servers, deploy EDR tools, and monitor for RansomHub’s signature file manipulations.
Akira: Multi-Platform Payloads and Virtualization Attacks
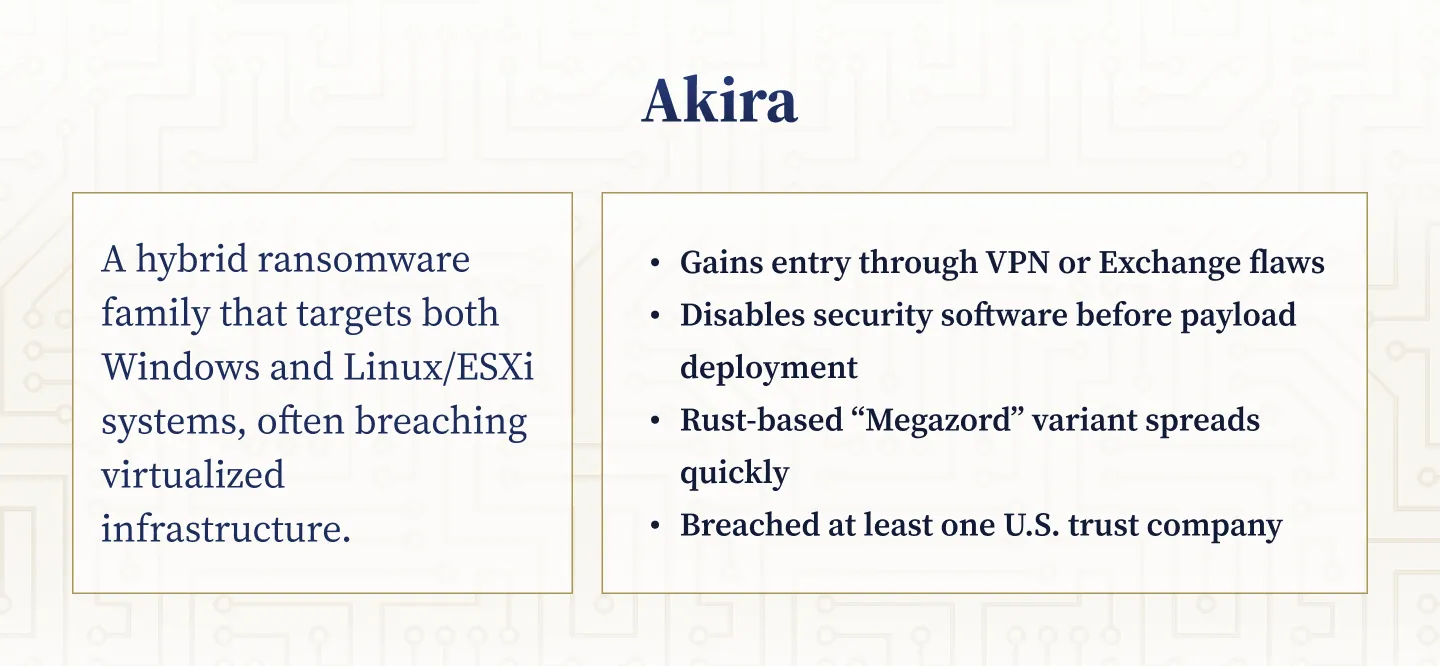
Technical Evolution
Akira, first identified in 2023, is notable for its hybrid ransomware targeting both Windows and Linux/ESXi environments. The group’s infection chain often begins with exploitation of VPN or Exchange vulnerabilities, or RDP accounts lacking MFA. Once inside, Akira affiliates disable security software, exfiltrate data using tools like FileZilla and RClone, and deploy ransomware payloads across all systems—including VMware ESXi hosts7,10.
Payloads and Encryption
Akira’s early payloads were C++ binaries (.akira extension), but by mid-2023, the group introduced a Rust-based variant (“Megazord,” .powerranges extension). The group uses double extortion, threatening to publish stolen data if ransoms are not paid.
Akira’s Financial Sector Breaches
Akira has breached at least one major U.S. trust company, and its ability to target virtualized infrastructure is a particular concern for banks and asset managers. FBI and Europol advisories recommend patching VPN/Exchange flaws and using EDR tools to detect Akira’s behaviors, such as PowerShell shadow-copy deletion and unique file extensions.
Play: Stealth, Lateral Movement, and Closed Negotiations
Initial Access and Lateral Movement
Play (PlayCRYPT) surfaced in 2022 and is known for its stealthy, “closed group” model. Affiliates use stolen or brokered remote administration credentials and exploit VPN and RMM vulnerabilities (notably FortiOS and Microsoft Exchange bugs) for initial access. Once inside, Play disables antivirus software and uses tools like Cobalt Strike, Mimikatz, and WinRAR for lateral movement, data theft, and encryption8.
Encryption and Negotiation
The ransomware encrypts every other 1MB chunk of files, appending the “.PLAY” extension. Victims do not receive a ransom note; instead, attackers initiate direct email contact to negotiate payment.
Play’s Banking Sector Incidents
Play has targeted manufacturing, healthcare, and at least one U.S. regional bank, with the FBI/CISA alert emphasizing the need for patching, network segmentation, and phishing-resistant MFA to prevent initial access.
%201%20(1).svg)
%201.svg)
THE GOLD STANDARD INCybersecurity and Regulatory Compliance
BianLian: Data-Leak Extortion and Tool Evolution
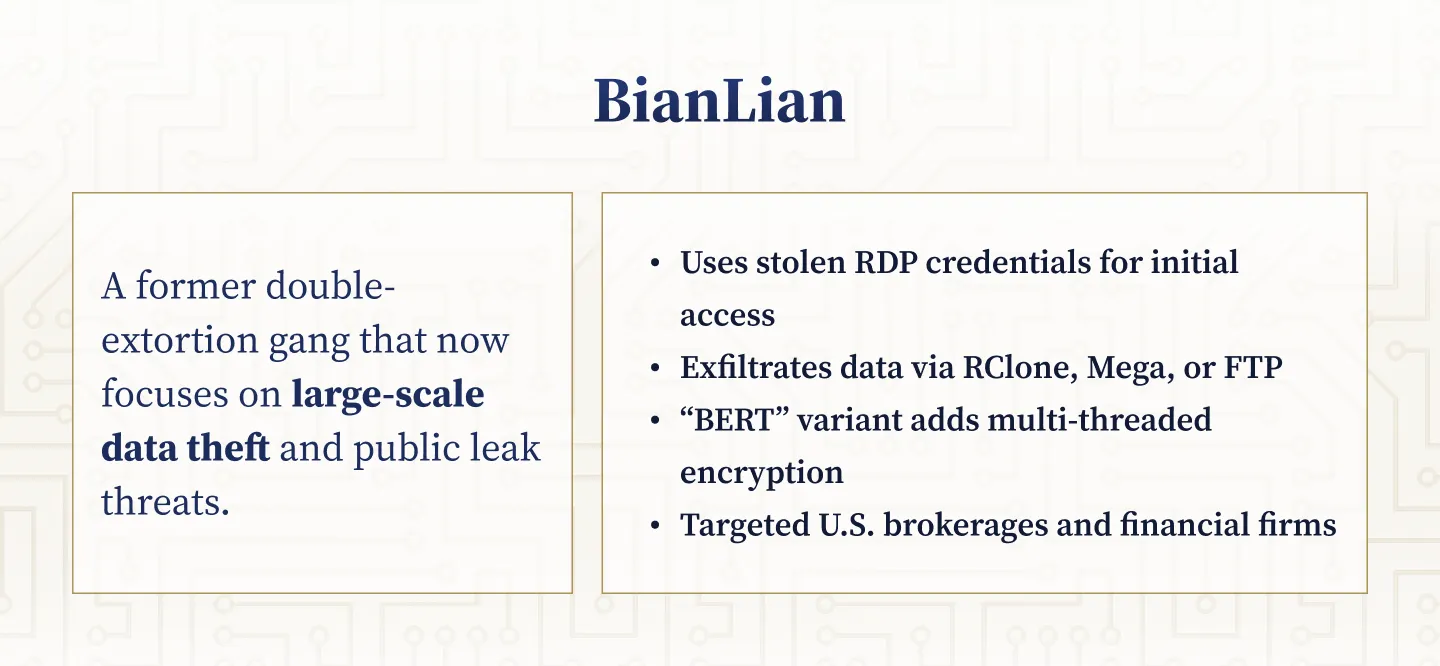
Shift from Ransomware to Data-Leak Extortion
BianLian, a Russian-based group, began as a double-extortion ransomware operation but shifted to pure data-leak extortion by early 2024. Affiliates use stolen or brute-forced RDP credentials for initial access, then deploy open-source tools (PowerShell scripts, scanners) for network mapping and credential harvesting. Data is exfiltrated via FTP or public cloud storage (Rclone, Mega)9,11.
Technical Innovations
Recent developments include the emergence of the “BERT” variant, which uses multi-threaded encryption and disables AV/defenses, mirroring BianLian’s tactics. BianLian’s affiliates quietly siphon terabytes of internal documents, threatening to publish them on leak sites if ransoms are not paid.
BianLian’s Financial Sector Impact
The group has targeted U.S. insurance brokerages and other financial firms. Financial institutions should focus on reducing exposed access channels, monitoring for large file transfers, and enforcing least-privilege access.
Royal / BlackSuit: Ex-Conti, Partial Encryption, and High-Value Targets

Attack Chain and Encryption Methods
Royal, later rebranded as BlackSuit, is operated by former Conti members and is known for highly targeted attacks on critical infrastructure, including banks. The group uses spear-phishing and RDP compromise for initial access, disables security software, and exfiltrates large volumes of data before deploying partial file encryption (encrypting alternating file chunks to speed up attacks and evade detection)12,13.
Negotiation and Ransom Demands
Royal/BlackSuit’s ransom notes require victims to negotiate via Tor, with demands ranging from $1 million to $11 million. The group’s persistence and ability to rebrand have allowed it to continue operations even after law enforcement disruptions.
Royal / BlackSuit’s Financial Sector Incidents
At least one U.S. bank has appeared on Royal’s leak site, and the group’s tactics are considered a top threat to the financial sector. Mitigations include network segmentation, disabling unnecessary remote access, and monitoring for outbound spikes of encrypted data.
Audit and Risk Management Imperatives for Financial Institutions
The technical sophistication and persistence of these ransomware gangs demand a multi-layered defense strategy. NETBankAudit recommends:
- Comprehensive internal and external vulnerability assessments, including authenticated scans and penetration testing to identify and remediate exposures before attackers do.
- Social engineering testing (phishing, pretext calling, onsite visits) to evaluate and improve employee awareness and response to credential-based attacks.
- Firewall, VPN, and remote access audits to ensure robust segmentation and minimize attack surfaces.
- Incident response and business continuity assessments to ensure rapid detection, containment, and recovery from ransomware events.
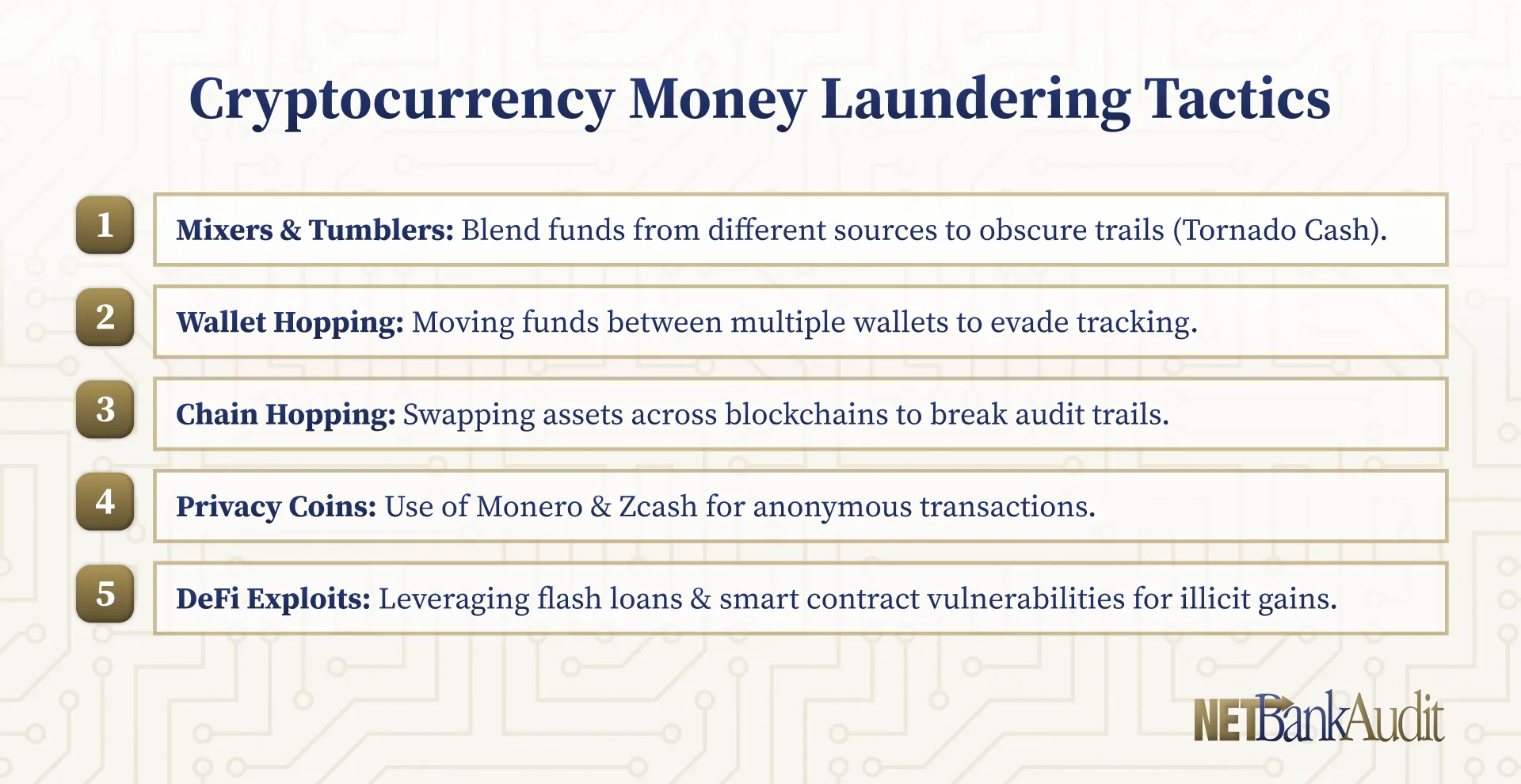
- For institutions holding or transacting in digital assets, a Crypto-Asset Safeguarding Risk Assessment to address the unique risks of cryptocurrency-based extortion and regulatory compliance.
NETBankAudit’s senior auditors and engineers use industry-leading tools and methodologies (COBIT, NIST, FFIEC) to deliver actionable, prioritized recommendations. Our team’s experience as former regulators, CIOs, and IT executives ensures practical, exam-ready results.
Complete our Request for Proposal for a cybersecurity audit or a crypto-asset safeguarding risk assessment, and take the first step toward a more secure and resilient future.
References
- U.S. Department of Justice, Office of Public Affairs. “U.S. and U.K. Disrupt LockBit Ransomware Variant.” justice.gov, 20 Feb. 2024.
- Cybersecurity and Infrastructure Security Agency (CISA) and FBI. “Scattered Spider (Cybersecurity Advisory AA23-320A).” cisa.gov, 16 Nov. 2023.
- Cybersecurity and Infrastructure Security Agency. “U.S. and International Partners Release Comprehensive Cyber Advisory on LockBit Ransomware.” cisa.gov, 14 June 2023.
- Reuters. “US Charges Five in ‘Scattered Spider’ Hacking Scheme.” Reuters, 20 Nov. 2024.
- Reuters. “UK, US and Australia Sanction Russian LockBit Ransomware Gang.” Reuters, 7 May 2024.
- Cybersecurity and Infrastructure Security Agency and FBI. “#StopRansomware: RansomHub Ransomware (Cybersecurity Advisory AA24-242A).” cisa.gov, 29 Aug. 2024.
- Cybersecurity and Infrastructure Security Agency, FBI, Europol, et al. “#StopRansomware: Akira Ransomware (Cybersecurity Advisory AA24-109A).” cisa.gov, 18 Apr. 2024.
- Cybersecurity and Infrastructure Security Agency, FBI, and ASD. “#StopRansomware: Play Ransomware (Cybersecurity Advisory AA23-352A).” cisa.gov, 4 June 2025.
- Cybersecurity and Infrastructure Security Agency, FBI, and ASD. “#StopRansomware: BianLian Ransomware Group (Cybersecurity Advisory AA23-136A).” cisa.gov, 20 Nov. 2024.
- Andres, Jaime. “A Spotlight on Akira Ransomware from X-Force.” IBM Security Intelligence, 2 May 2024.
- Singal, Nidhi. “Trend Micro Flags BERT: A Rapidly Growing Ransomware Threat.” CSO Online, 9 July 2025.
- Cybersecurity and Infrastructure Security Agency and FBI. “#StopRansomware: Blacksuit (Royal) Ransomware (Cybersecurity Advisory AA23-061A).” cisa.gov, 27 Aug. 2024.
- Cybersecurity News. “Royal/BlackSuit Ransomware: The Ex-Conti Rebrand.” cybersecuritynews.com, 2024.
.avif)

.svg)

%201.webp)



.webp)
%20(1).webp)

.webp)

.webp)
.webp)
.png)

.webp)

.webp)











.webp)



.webp)

%201.webp)
.webp)
%20(3).webp)


.webp)


%20Works.webp)

.webp)




.webp)
%20(1).webp)

.webp)










.webp)
.webp)

.webp)
.webp)
.webp)
.webp)
.webp)
.webp)
%201.svg)